Companies are shifting their systems and forms to the cloud. As such, new security standards have been introduced to help defend the cloud workloads against hackers. You can ultimately manage the risk and compliance of the workloads of the information you bring to the cloud with the help of reliable cloud security companies.
What is Cloud Security? Why do you need it?
When you build applications, migrate them, and modernize the business, you start with data. With all the risks that you deal with, the kind of data you transfer matters. It can be classified data, public data, or delicate data that may deal with private information. Acknowledge all those factors and choose a secure form around what your data security structure needs.
Cloud security is the system of shielding cloud-based data, applications, and infrastructure from possible cyberattacks.
Here are the four best cloud security companies.
CloudPassage
CloudPassage is a security software as service provider that offers easy, effective solutions to protecting servers hosted in elastic clouds. The CloudPassage halo safety platform is purpose-built to control security on Linux servers in elastic cloud settings. Security features built on the halo platform, such as vulnerability management and host-based firewall administration, are delivered elastically. That means they automatically supervise cloud server dynamics like cloud bursting.
These capabilities were created to help server officials address protection in the fast-growing cloud server market. It’s well known that server compromises result in identity theft denial. The halo solutions are a software as well as a service, so they are easy to deploy. It provides file integrity monitoring, software vulnerability assessment, log-based intrusion detection, secure configuration assessment.

LaceWork
LaceWork is focused on cloud security for the modern age of cloud-centric companies. They take a very precise machine language approach to taking all the data in from machines or cloud integrations and quantifying normal behavior. LaceWork has created a platform from the ground up to offer a much more efficient and highly integrated solution and system.
LaceWork does a broad set of things. They span multiple categories from compliance for the cloud, configuration for the cloud, anomaly detection, build time to run time. Within each of these categories, they use a core technology called polygraph. It allows them to find and identify things. LaceWork is a cloud security company that allows you to view all the data, the context, and the efficacy of all that data.
Tenable
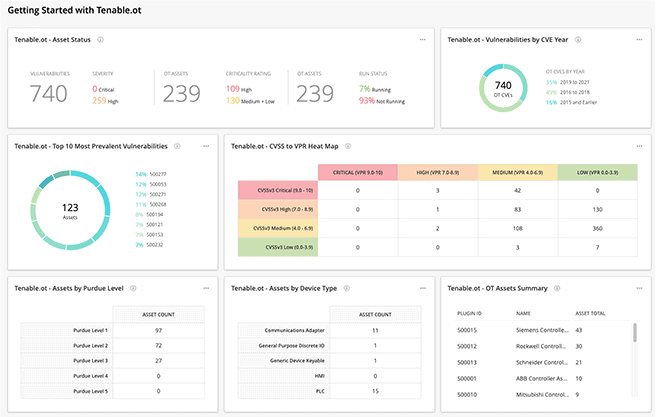
Tenable is a vulnerability management software company. They make several different tools for identifying network vulnerabilities. Tenable is a cloud-based vulnerability management tool that gives IT security teams a complete picture of vulnerabilities affecting their network. This security company works in real-time to constantly provide the most up-to-date information about potential security threats. They offer important contextual information, suggested solutions based on multiple data sources. Tenable comes with pre-built dashboards and reports. You can easily customize dashboards and reports to suit your own business.
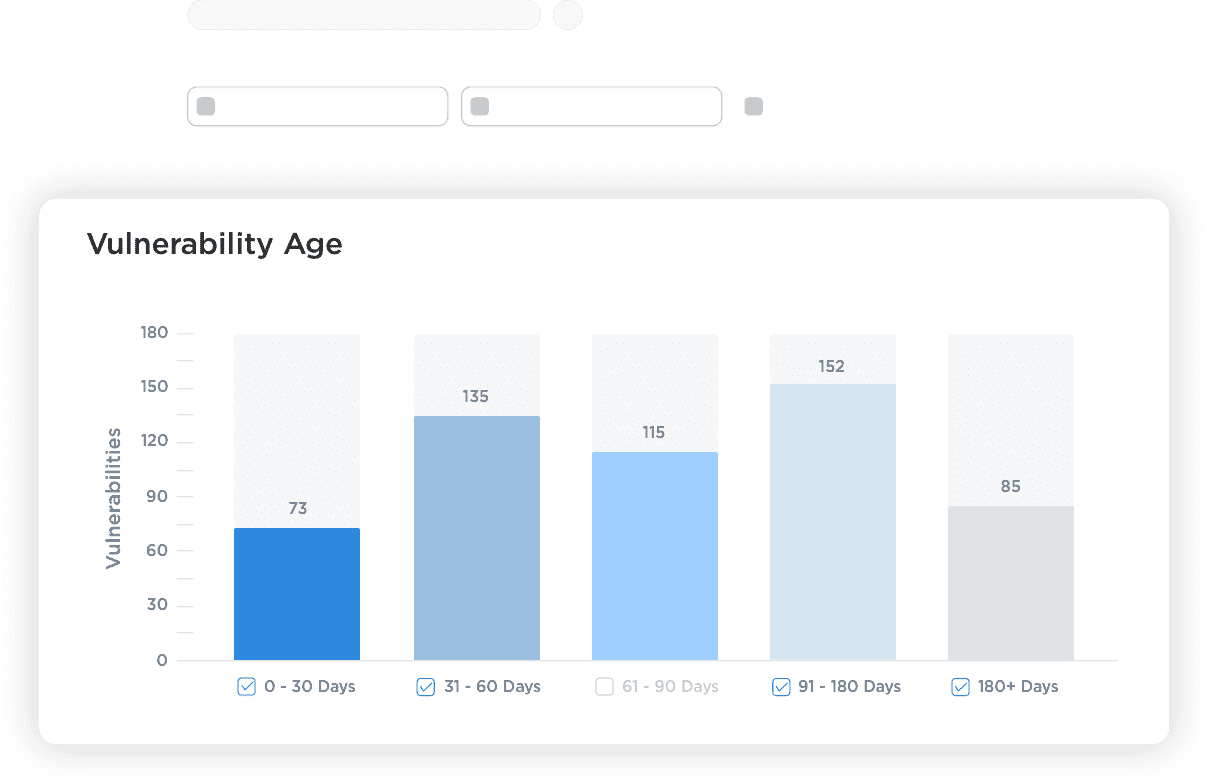
Their core function is vulnerability management which helps users identify vulnerabilities with the help of the intuitive user interface. You can customize the dashboard and see a big picture view of your assets, total vulnerabilities, scan coverage, and highest risk vulnerabilities. Tenable also shows which assets they affect and offer solutions for remediation. Another great feature is their risk-based approach to prioritizing vulnerabilities. With vulnerability data science and threat intelligence they highlight vulnerabilities that have greater risks.
Qualys
Qualys cloud platform is a single platform that constantly monitors every asset on your network, whether a personal mobile phone, test server, public cloud, container decommissioned laptop or Wi-Fi-connected gadget. Qualys can find and categorize all of your assets and alert you to any changes made. They are gathering data from remotely deployed self-updating sensors and bringing data settings into the cloud platform.
Qualys provides continuous visibility into the global hybrid IT environment. This cloud security corporation automatically transfers customizable warnings regarding the most crucial issues for prioritized response and fast action. The search engine makes fact-finding or quarantine assents easy to find. The great thing about Qualys is that it instantly shows you the threat on the customizable dashboard. It provides a range of attack surface options mapped to the vulnerabilities.
Conclusion
Cloud security companies give their clients power over the ever-expanding outline that comes with running services and cyber business. Each of these cloud security companies has a different toolset that creates information silos and unique methods for consuming security-related data. These cloud security companies give you a platform with high clarity to manage important cybersecurity concerns you may have. You can find the biggest differentiation between cloud security companies in the many features they offer, and how these innovations are divided among setting plans. They guarantee to keep your business and data secure.
